Updated: This article includes insights from a spokesperson at Ledger.
A Brazilian cybersecurity expert has unveiled a sophisticated scheme involving counterfeit Ledger devices designed to extract cryptocurrency from unwitting users.
Summary
- A Brazilian researcher discovered a counterfeit Ledger Nano S Plus that features modified firmware intended to steal user recovery phrases.
- Examinations of the fake device revealed unauthorized WiFi and Bluetooth components, as well as a secondary manufacturer’s chip concealed under altered markings.
- The operation employs a misleading QR code on the packaging to entice users into downloading a malicious application designed to circumvent official security measures.
The researcher, who operates under the pseudonym “Past_Computer2901,” posted his findings on Reddit, having purchased what appeared to be a legitimate Ledger Nano S Plus from an online marketplace in China.
Although the packaging and pricing aligned with official retail standards, the unit failed a “Genuine Check” when connected to the authentic Ledger Live application.
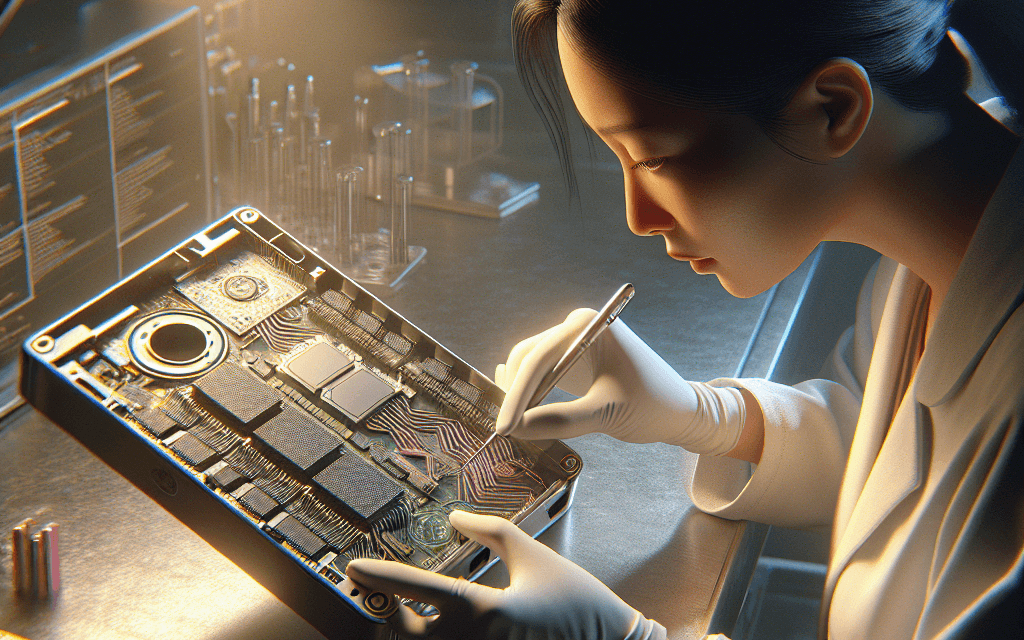
This warning sign prompted a thorough physical examination of the device, revealing that alterations had been made to its internal components, including the addition of WiFi and Bluetooth antennas—features that do not belong to the original model.
Compromised Hardware and Deceptive Tactics
The counterfeiters are exploiting these tampered devices to target new cryptocurrency investors through a deceptive setup process.
A QR code included in the packaging misdirects users to a fraudulent version of the Ledger Live application, allowing the app to circumvent security alerts and falsely verify the hardware’s authenticity.
Once users enter or create their seed phrases, the compromised firmware captures this sensitive information, enabling attackers to drain the connected wallets at will.
“I aim to inform rather than cause alarm; I was genuinely taken aback by the vastness of this scheme,” the researcher expressed.
In-depth analysis of the unit showed that the scammers took extensive measures to conceal their deception, including the removal of original chip markings.
Counterfeit Ledger device. Source: Reddit.
Initially, the device identified itself as a Nano S Plus 7704 during the boot sequence, but it ultimately revealed Espressif Systems, a semiconductor manufacturer based in Shanghai, as the real producer.
These modifications fundamentally compromise the security principle of Ledger products, which are designed to keep private keys completely offline.
“When making purchases from a marketplace, Ledger strongly advises users to confirm the seller’s legitimacy. Moreover, downloads of Ledger Wallet applications should only come from official sources. This incident involved counterfeit hardware and a fake app meant to simulate the onboarding process, distributed through unverified channels,” a Ledger spokesperson noted in a statement to crypto.news.
“Remember, Ledger will never ask users for their 24-word recovery phrase. If anyone claiming to be Ledger, or any app that presents itself as a Ledger application, requests these phrases, consider it a scam,” they added.
This revelation comes on the heels of another incident earlier this month, whereby a fraudulent application bypassed Apple App Store security using a bait-and-switch technique. This malicious software successfully tricked over 50 individuals into revealing their recovery phrases, leading to a theft of $9.5 million before the app was ultimately taken down. Apple has since removed the app due to its malicious functionality.
“Exercise caution. Only download Ledger Live from ledger.com, and purchase hardware exclusively from ledger.com. If your device does not pass the Genuine Check, cease all usage immediately,” the researcher cautioned.