Your Ethereum wallet serves as a public ledger, exposing every transaction you’ve conducted — detailing who you’ve sent funds to, the amounts transferred, and the timestamps of these actions. In a world increasingly concerned with digital privacy, privacy pools offer a powerful solution to conceal these connections. In this article, we’ll explore how to effectively use privacy pools to secure your financial activities on the Ethereum network.
Key Insights
- A privacy pool is a smart contract designed to obfuscate the link between sender and recipient on Ethereum through fund mixing and the employment of zero-knowledge proofs.
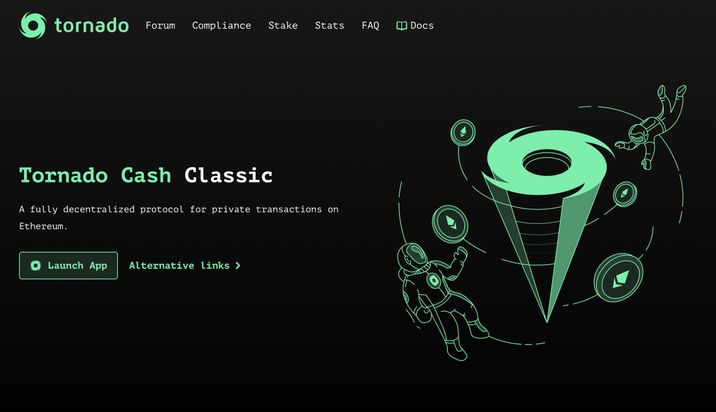
- Traditional privacy pools (like Tornado Cash) operate in four steps: generating a secret note, making a deposit, waiting for the anonymity set to expand, and finally withdrawing to a fresh address.
- Next-generation privacy pools implement a compliance framework that allows users to prove their funds are clean without revealing the specifics of their individual deposits.
- These new pools mark a departure from traditional mixers by differentiating between “clean” and “tainted” funds, minimizing the chance of innocent users being flagged by exchanges.
What Is a Privacy Pool?
A privacy pool in the Ethereum ecosystem is essentially a smart contract enabling users to hide the sender-recipient relationship in Ethereum transactions. It achieves this by mixing various users’ funds and leveraging the power of zero-knowledge proofs.
In essence, think of a privacy pool as a crypto blending service utilizing sophisticated technological means. But why is this service necessary?
The Importance of Privacy Pools
Many might wish to shield their transactions from external scrutiny for various reasons — be it personal privacy, receiving a salary in cryptocurrency, or simply wanting to maintain confidentiality in a public system. Utilizing a privacy pool supports your fundamental right to privacy.
As Vitalik Buterin states, privacy equates to freedom and serves as a critical component of decentralization. While blockchains are public by nature, this does not negate individual privacy rights.
All transactions on the Ethereum network are traceable, meaning that once someone identifies your addresses, they can observe your entire balance and transaction history. This has made users vulnerable to various scams, including “address poisoning,” where individuals exploit this visible data to compromise your wallet security.
Read more: How Address Poisoning Scams Can Target Your Crypto Wallet
Thanks to privacy pools, you can safeguard your cryptocurrency and personal details. Here’s an overview of how a classic privacy pool operates.
Classic Privacy Pool Mechanics
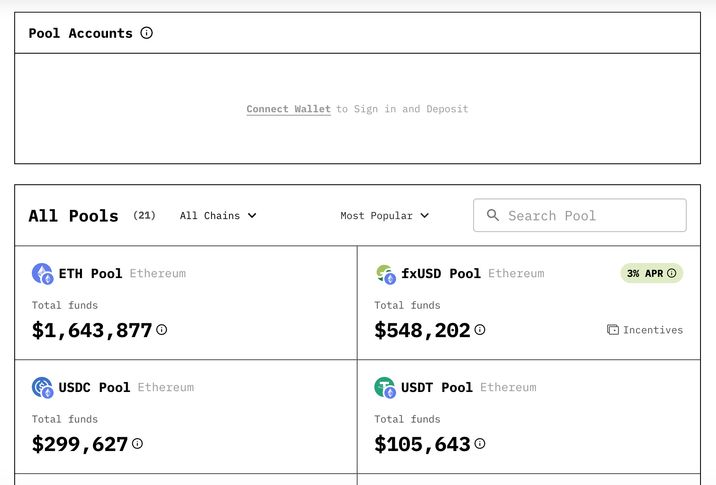
The most renowned privacy pool, Tornado Cash, is a fully decentralized protocol that supports numerous blockchain networks. Let’s break down its operational mechanics:
Step 1: Secret Note Generation
Before making a deposit, you’ll connect your crypto wallet, and either your wallet or the privacy pool itself will generate a secret note. This note will be your only proof of ownership for the deposit, resembling something like this:
note = tornado-eth-10-0×8f3b…e1
If you lose this note, you will be unable to access your funds since it isn’t recorded on the blockchain.
Step 2: Depositing Funds
Next, you’ll make a deposit — say, 1 ETH or another predetermined sum — into the pool’s smart contract. The contract will accept your deposit, record a unique cryptographic fingerprint of your note, and place it in the deposit list, meaning the contract cannot associate the deposit with its owner.
Step 3: Mixing Deposits
For the privacy pool to work effectively, it needs numerous users. Therefore, you may have to wait hours or even days for additional deposits to accumulate. The more deposits there are, the harder it becomes to correlate entry and exit transactions.
Step 4: Withdrawing to a New Address
Finally, when you’re ready to withdraw, you’ll enter your secret note. The system will generate the necessary cryptographic proof and submit it to the smart contract. If your proof checks out, your funds will be dispatched to your designated address.

Next-Generation Privacy Pools
Traditional mixers merely obscure the connection between sender and recipient by pooling funds from numerous users. However, this model has a significant flaw: it treats “clean” and “tainted” funds equally. Consequently, if illicit assets enter the pool, everyone withdrawing these funds becomes equally suspect. As a result, many centralized services and exchanges often flag or block funds that have passed through these mixers.
Privacy Pools represent a modern architecture that maintains user anonymity while allowing participants to certify that their assets do not originate from suspected illicit activities. The key feature here is that when withdrawing funds, users can generate cryptographic proof to indicate that their deposit belongs to an approved set of transactions while concealing the exact deposit and their identity.
How Do Next-Generation Privacy Pools Operate?
A user initiates the process by depositing funds into the smart contract, akin to how traditional mixers function. This contract records a cryptographic commitment representing the deposit, ensuring it cannot be directly linked to the user’s wallet. Subsequently, independent analysis services or Association Set Providers (ASPs) compile a roster of acceptable deposits, distinguishing them from known fraudulent or sanctioned funds.
When a user wishes to withdraw, they generate a cryptographic proof that confirms two things: firstly, they control one of the deposits within the pool, and secondly, that this deposit belongs to an approved association set. The beauty of this proof is that it does not disclose which specific deposit is involved, thus maintaining privacy. Observers can verify that the funds are approved without knowing the specifics of the transaction.

This dual-layer approach strives to balance both privacy and transparency. Users can maintain their financial confidentiality as their transactions remain anonymous within the pool while simultaneously being able to verify that their funds do not originate from suspicious sources. This innovative method is increasingly proposed as a viable solution for privacy amidst growing regulatory and compliance expectations in public blockchains.
Strategies for Minimizing De-Anonymization Risks in Privacy Pools
Even with robust cryptography employed by a privacy pool, user behavior can still inadvertently expose links between deposits and withdrawals. Most de-anonymization efforts in blockchain analysis arise not from cracking the protocol but from studying transaction timing, address relationships, and patterns of behavior. Below are practices that can help diminish the risk of linking a deposit to a withdrawal:
- Use a new address for withdrawals: Always withdraw to a different address than the one used for deposit. Ideally, generate a new wallet address that has never engaged in prior on-chain activity.
After withdrawal, make sure not to transfer funds back to addresses related to your depositing wallet. Blockchain analytics can easily detect clusters of addresses operated by the same user.
- Introduce a delay between deposits and withdrawals: Quick withdrawals after depositing increase the chances of observers connecting the two transactions. A delay — ideally until multiple other deposits have been made — enhances the anonymity set.
- Wait for a larger anonymity set: The higher the number of deposits between your deposit and withdrawal, the more challenging it becomes to statistically attribute them.
- Avoid unique transaction patterns: Regular behavior patterns — like consistently withdrawing after similar intervals or following the same sequence of DeFi actions — can lead to identifiable fingerprints.
- Separate gas funding from identifiable wallets: If the withdrawal transaction is funded by an address tied to your identity, analytics can link the transactions back to you. It’s best to use gas funding sources that are difficult to trace back to your primary wallet.
- Avoid immediate interactions with centralized exchanges after withdrawal: Transferring funds directly to an exchange account directly linked to your identity can negate the privacy protections offered by the pool.
- Avoid combining mixed funds with traceable assets: If funds received from a privacy pool are merged with known addresses, analysts can reconstruct transaction histories and ownership.
- Utilize distinct infrastructure for both deposits and withdrawals: Subtle metadata like RPC endpoints, wallet fingerprints, or relayer usage can sometimes establish correlations between transactions.
Frequently Asked Questions
What distinguishes a privacy pool from a crypto mixer?
Traditional crypto mixers merely obscure transaction links through fund mixing. Privacy pools enhance this mechanism by integrating systems that permit users to certify that their assets are not tied to illicit sources, all while maintaining user anonymity.
Are privacy pools legal?
The legality surrounding privacy pools can vary by jurisdiction. Generally, the technology itself is legal, but services facilitating anonymous financial transactions may be subject to governmental regulations or restrictions. It is advisable for users to familiarize themselves with local laws before utilizing privacy-focused solutions.
Do privacy pools ensure total anonymity?
No privacy solution can completely assure anonymity. While the cryptographic framework hinders direct transaction linking, external elements such as user behavior, interactions with exchanges, and timing can diminish privacy protections. Privacy pools significantly enhance transaction confidentiality, but users should exercise caution.